Hello, my dear readers who have been missing the posts! I know you've all been waiting for brilliant posts over the past two years. But both I and d_x have been busy with matters that, to be honest, are second only to saving the world... or maybe not. Today's topic is CEN/XFS, a specific and extremely necessary standard for interacting with banking equipment, more specifically, the way to analyze XFS API calls on Windows. If you still don't know what CEN/XFS is (not to be confused with XFS, the file system), then you probably had a blissful life without a headache. But for those who are ready to dive into this swamp - welcome.
Continue reading "Analyzing XFS API Calls"
20 years of payment processing problems
Thanks to @yarbabin for the logo
Electronic payment systems have existed on the Internet for a long time, and some bugs in them are twenty years old. We've found critical vulnerabilities allowing us to steal money and drive up the balance. Today we will analyze typical implementations of payment processing and related security issues.
Reading another process memory via page combining in Windows 10
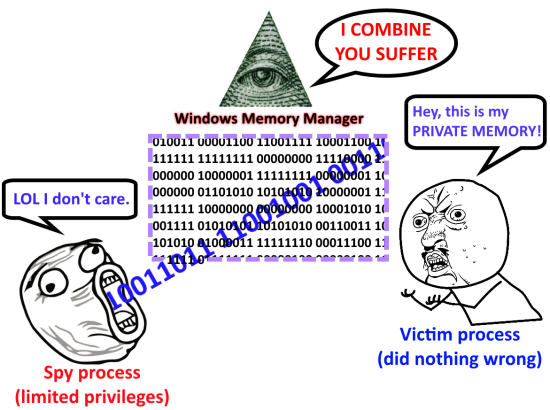
It's not as scary as it looks, and you're not able to read memory of any arbitrary process. At least without some preconditions. The main vulnerability is almost completely fixed now. Therefore, this post is rather a historical reference and is offered for your self-improvement. In addition, to my knowledge, no one has yet described the exploitation method that I offer.
To begin with, Microsoft was notified about this problem around a year and a half ago. In response, they told me the vulnerability had been fixed mostly, and that I can publish my small research.
So let's begin. Windows 8.1 and Windows 10 brought a memory or page combining feature at some point (the Windows Internals, 7th edition, part 1 book describes it in detail). The idea is quite simple: every 15 minutes the operating system searches the physical memory for pages with the same content and combines them into a single one in order to save RAM. Those processes that owned the same pages receive links to a new shared page with the read-only and copy-on-write attributes. If any process changes its page, a copy-on-write exception occurs, and the system copies the page again to physical memory, and the process receives an individual copy of this page.
Continue reading "Reading another process memory via page combining in Windows 10"
Getting acquainted with ARM Cortex-M

Today we'll discuss 32-bit microcontrollers with ARM Cortex-M cores and, in particular, STMicroelectronics (aka ST) controllers. This post will describe how to develop for these controllers, which development environments available, and how to use some popular libraries. If you are interested in Arduino development, but 8-bit AVR is no longer enough for you, and you want something more, then this post is for you.
Follow-up: filled NTFS partition cleanup
In the previous post Filling up NTFS partition forever without admin privileges I described the method to fill all free space on an NTFS partition without administrator privileges and without creating any large suspicious files. However, "forever" in the title was too strong a word, so I continued to search for solutions to cleanup the clogged $Secure file. Finally, I found this can be done quite simply: you need to use the standard Windows CHKDSK utility! I would've never thought that it had such a feature. Apparently, it was added in around 2009 in the KB919241 update.
Filling up NTFS partition forever without admin privileges

NTFS is an advanced file system that is one of the main parts of all modern Windows operating system versions. This file system supports logging, it has the ability to recover data, advanced security, file streams and many other features. However, sometimes with rich features you get problems that were absent in older file systems like FAT32.
Continue reading "Filling up NTFS partition forever without admin privileges"
Writing macros with GUI for Microsoft Word like a PRO [Part 2, final]
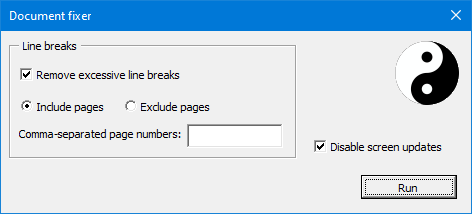
Let's dive deeper into the topic of macros in Microsoft Word. We will add the user interface for our macro, which replaces two or more consecutive line breaks with a single one. Why would you ever need some kind of interface for a macro? Well, for example, you want to remove extra line breaks on all pages of the document, except for some specific ones. The interface would allow you to specify the page numbers that you want to skip during processing (or vice versa, only process specified pages). This is the functionality we will implement.
Continue reading "Writing macros with GUI for Microsoft Word like a PRO [Part 2, final]"
Writing Macros for Microsoft Word like a PRO [Part 1]
You may have the feeling that the Word macros are quite useless. Who needs them anyway? Well, sometimes they are used in malware... Moreover, they are written in a long forgotten VBA (Visual Basic for Applications, which is somehow limited Visual Basic 6 in an interpreted form), eeww!
But in fact, after all, many people may sometimes need to write a report in Word, or issue a paper, or write a CV before sending it to their dream company... For some people, their job is working in Word itself. Often, various documentation systems can export pages to doc or docx formats that your customers ask for. And it often happens that exported documents look awful, you have to fix them manually every time after export.
Working in Word often involves performing some repetitive actions, which can be sometimes (but not always!) solved by correctly setting and applying styles, as well as using templates. How do you automate everything else? This is where these very macros come to our aid.
Continue reading "Writing Macros for Microsoft Word like a PRO [Part 1]"
Writing simple Nessus plugin

One of the key aspects of penetration testing is the automation of routine actions. Someone writes standalone programs for this, but now there are many products that allow you to extend their functionality with the help of additional modules. An example of a free vulnerability scanner with custom modules support is OpenVAS, but this article is about Nessus, which isn't free, but in my humble opinion, finds more and generates fewer false positives (although OpenVAS started as a fork of Nessus, but that was a long time ago). Let's get started.
Continue reading "Writing simple Nessus plugin"
Pentest 101: Content bruteforcing lists
When it comes to black-box testing of web applications, one of the main things is to search through possible web paths to find new entry points and “forgotten” data. That is, any list of popular directory names (like /uploads/) and files (data.txt, file.php, etc.) is taken and a sequential search of valid paths is performed. The technique is well-known, old, there are many utilities to exploit it, many public lists of such paths. Among the most popular are the following utilities:
- dirb (http://dirb.sourceforge.net/)
- wfuzz (https://github.com/xmendez/wfuzz)
- DirBuster (https://sourceforge.net/projects/dirbuster/)
- nikto (https://github.com/sullo/nikto)
- dirsearch (https://github.com/maurosoria/dirsearch)
- nmap (http-enum module) (https://nmap.org)
- Metasploit Framework (dir_scanner and files_dir modules) (https://www.metasploit.com/)
- Burp Suite (using Intruder) (https://portswigger.net/burp)
Lots of them...
Personally I prefer wfuzz (pretty fast, convenient filtering of web server responses by several criteria), or Burp Suite.
Continue reading "Pentest 101: Content bruteforcing lists"